Fix Security Issues Overnight With Automated Remediation

Security drift can happen in a single day. A patch fails, encryption gets turned off, or an agent stops reporting. That does not mean your tools are broken. It means real environments keep changing, and small gaps can create security vulnerabilities if nothing pulls systems back to baseline.
Automated remediation restores devices and controls to an approved baseline when they drift. Instead of relying on someone to manually catch and fix every issue, the system detects the change and returns the endpoint to the state your team already approved.
For small and mid-market teams, that matters because drift is constant and manual follow-up does not scale. Zip helps keep Jamf, Intune, and endpoint security tools enforced, visible, and provable over time so lean teams can reduce security threats, respond faster to potential threats, and protect sensitive data.
Key Takeaways
- Drift starts right after deployment, so controls need continuous enforcement instead of occasional checkups.
- Automated remediation restores endpoints to approved baselines as soon as they fall out of compliance.
- Self-healing security reduces manual policing by turning common fixes into repeatable workflows.
- Continuous policy enforcement maintains consistent device management and endpoint security across the fleet.
The Hidden Problem: Security Drift
Even strong security controls drift over time if nothing keeps them enforced.
What Causes Drift In Real Environments
Security drift usually comes from normal change, such as:
- Users changing local settings
- Patches failing or only partially installing
- New apps or browser extensions appearing outside the baseline
- Policies apply differently across MDM, EDR, and identity tools
- Devices being replaced, re-enrolled, or reassigned
Zip gives your team one place to see device posture, policy state, and drift across existing tools, while Jamf and Intune stay in place. That visibility helps teams identify vulnerabilities earlier, support Jamf compliance, and address configuration gaps before they turn into security incidents.
Why Drift Turns Into Risk Quietly
Most drift stays hidden until an audit, customer review, or incident exposes it. In fact, we recently conducted a survey of over 300 companies and found that 64.5% of companies found unsecure devices that they thought were covered, and of those who found gaps, almost half of them discovered the unsecure devices during an audit. 1 in 3 companies only discovered drift after a breach.
That is what makes drift risky—it can be hard to see without full visibility into your security. The real value comes from quickly finding drift, fixing it, and proving the control is back in place. That is essential for regulatory compliance, internal reporting, and day-to-day event management when teams need clear answers fast.
Why Manual Remediation Breaks At Scale
Manual remediation sounds manageable in theory. In practice, it creates too much operational overhead for lean IT and security teams to sustain.
Alert Fatigue Is A Workflow Problem
Teams do not struggle because they do not care. They struggle because the workflow breaks down.
Too many tools create too many queues, for example:
- One system flags an unhealthy sensor
- Another shows an encryption exception
- A third point to the enrollment issue behind both
Response Time Depends On Humans
Drift often shows up at the worst possible time, such as:
- Nights
- Weekends
- Onboarding rushes
- Audit prep
- The middle of everything else
When remediation depends on a person being available, the gap stays open longer. Backlogs grow. The urgent queue becomes the normal queue. Security posture starts to depend on human bandwidth.
Zip’s managed IT and security operations approach addresses this gap directly. It helps teams detect issues early, resolve them automatically when appropriate, and escalate when needed. That creates a more sustainable model than waiting for every issue to turn into a manual ticket.
Inconsistent Policy Enforcement Creates Exceptions
Manual fixes also create inconsistency. In real environments:
- One admin reapplies a profile
- Another document, an exception, and plans to revisit it
- An MSP handles the same issue differently for a different customer
- A temporary workaround stays in place because something else feels more urgent
With Zip, remediation becomes an enforceable guardrail instead of a string of one-off cleanups. When a device slips, the goal is to push it back to the approved state, not just note that it drifted. That kind of consistency helps teams mitigate risk without relying on constant follow-up.
How Automated Remediation Works
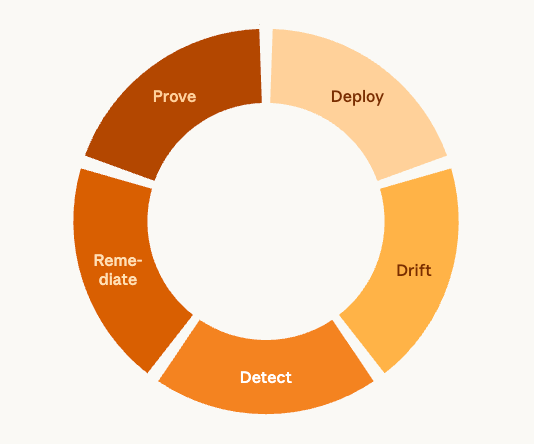
Automated remediation works best when it follows a clear, repeatable process that keeps endpoints aligned with approved security standards over time.
Continuous Monitoring
The first step is visibility into the current state.
That includes device health, policy status, encryption state, patch posture, enrollment state, and endpoint sensor health. NIST’s continuous monitoring model emphasizes visibility into both assets and control effectiveness because current-state awareness supports better risk decisions.
Zip fits naturally here. It brings together signals from device management, endpoint security, and related systems so you can see what is happening without stitching together half a dozen views by hand.
Drift Detection
Drift detection compares the current state to the approved baseline.
That distinction matters. Detection is not “something looks strange.” It is “this device no longer matches the policy and control state we approved.”
That is why strong baselines matter. Using CIS Benchmarks provides prescriptive, consensus-based configuration guidance that teams can apply and maintain over time.
Automated Correction
Once drift is confirmed, automated remediation applies a pre-approved response.
That can include reapplying a profile, restoring a required setting, re-enabling a protection, prompting re-enrollment, or confirming that an endpoint agent is healthy again. The goal is to use safe, known actions to return the device to the state your team already approved.
This feature also supports a safer rollout model. Teams can start in detect-only mode, learn what common drift looks like in their environment, and move toward enforcement once the baseline and remediation paths are well understood.
Continuous Policy Enforcement
The goal is not one-time compliance. The goal is ongoing alignment. Controls need to stay enforced as devices, users, tools, and settings change.
That is why this matters for BOFU buyers. If your team already uses Jamf, Intune, CrowdStrike, and identity tooling, the next question is not “what other tool can I buy?” It is “how do I keep this stack working as intended over time?”
Want to see what self-healing enforcement looks like in your environment? Book a demo.
Where Automated Remediation Pays Off First
Automated remediation delivers the most value in the day-to-day areas where lean teams usually lose the most time and consistency.
Stronger Endpoint Security Without More Tickets
If an EDR sensor becomes unhealthy or requires protection, stop running; automated remediation shortens the time between drift and correction. That means fewer lingering gaps and fewer manual cleanup tickets.
Zip supports this directly by helping teams simplify detection, prevention, and remediation workflows across their stack.
Less Manual Policing For IT And Security Departments Of One
Lean teams do not need more dashboards to watch. They need fewer repetitive checks.
That is where automated remediation helps most. It turns recurring device and policy issues into workflows instead of interruptions. Zip’s positioning for IT managers and IT teams centers on this need: continuously enforced controls without the enterprise-scale staffing required.
Faster Containment Of Common Drift Scenarios
Not every issue becomes a major incident. But common drift scenarios still matter, including:
- Missing encryption
- An unhealthy endpoint agent
- A missing MDM profile
- Local configuration that no longer matches policy
Automated remediation reduces the time spent on these routine problems. Zip’s device management approach focuses on baselines, visibility, and enforcement across both Windows and macOS, where many of these issues first appear.
Audit Readiness That Doesn’t Start The Week Before
A strong security story is easier to tell when your evidence stays up to date.
Zip’s compliance positioning focuses on making posture easier to explain and prove over time. That puts teams in a better position than relying on screenshots, memory, and last-minute verification. It also supports smoother regulatory compliance by making enforced controls easier to show to auditors, customers, and leadership.
Proactive Security In Action: A Simple Example Workflow
A simple workflow shows what self-healing security looks like in practice.
A Windows laptop drifts out of compliance because:
- Encryption is disabled
- The endpoint sensor stops reporting correctly
From there, the system follows a defined process:
- Detect Drift: Compare the device’s current state against the approved baseline.
- Trigger Remediation: Apply the pre-approved fix, such as reapplying configuration, restoring required settings, and validating endpoint security health.
- Record Evidence: Log what changed, when it changed, the action taken, and the current status after remediation.
For teams managing mixed environments, this matters because the process stays consistent across tools. Instead of relying on memory, every fix follows a defined pattern. That is what a practical proactive security strategy looks like in action.
Proactive Cybersecurity Turns Overnight Security Into A System
More monitoring alone can still leave your team with more alerts and more follow-up. Proactive security works differently. It relies on enforced baselines, automated remediation, and continuous policy enforcement to address issues quickly and consistently.
That matters because drift is normal. In real environments, settings change, tools fall out of alignment, and endpoint posture shifts when nobody is watching. Zip helps lean teams turn that reality into a manageable system by making it easier to see, enforce, and prove controls across endpoints, without adding more manual work.
Ready to make remediation automatic and posture provable? Explore Zip’s managed IT and security operations today.
FAQs About Automated Remediation
1. Does Automated Remediation Replace Jamf, Intune, Or CrowdStrike?
No. It works alongside them. Zip sits above existing tools and helps keep policies enforced, visible, and easier to prove over time, rather than replacing core systems like Jamf or Intune.
2. Why Does Automated Remediation Matter For Proactive Security?
It matters because strong security depends on more than visibility. Teams need systems that can detect drift, correct it quickly, and maintain proof over time. That is what makes automated remediation a practical part of a broader proactive security strategy.
Related articles

Why Automated CIS Benchmark Enforcement Is Stronger Than Manual Security

Ready to Work in Minutes with Zero-Touch Security