No IT Team or MSP Required
Your entire security program. Done for you.
Pass security audits and customer security questionnaires. Get secure in 14 days.
Security doesn't have to be complicated
We have a three-step plan that gets you there. No endless projects. No security expertise required.
Step 01
Get Full Control
See every person and device in your company, and manage access from one place.
- Know exactly who can access your systems and from which devices
- Lock or wipe lost or stolen laptops instantly
- Cleanly remove access when employees leave
Step 02
Get Security Deployed
Zip sets up protection on every device and account. The right settings, configured automatically.
- Your devices get set up the right way: encryption, recovery keys, and security settings handled automatically
- Two-factor authentication (2FA) enabled and enforced across your company
- CrowdStrike endpoint detection and response (EDR) deployed on every device, with clear visibility
Step 03
Stay Protected
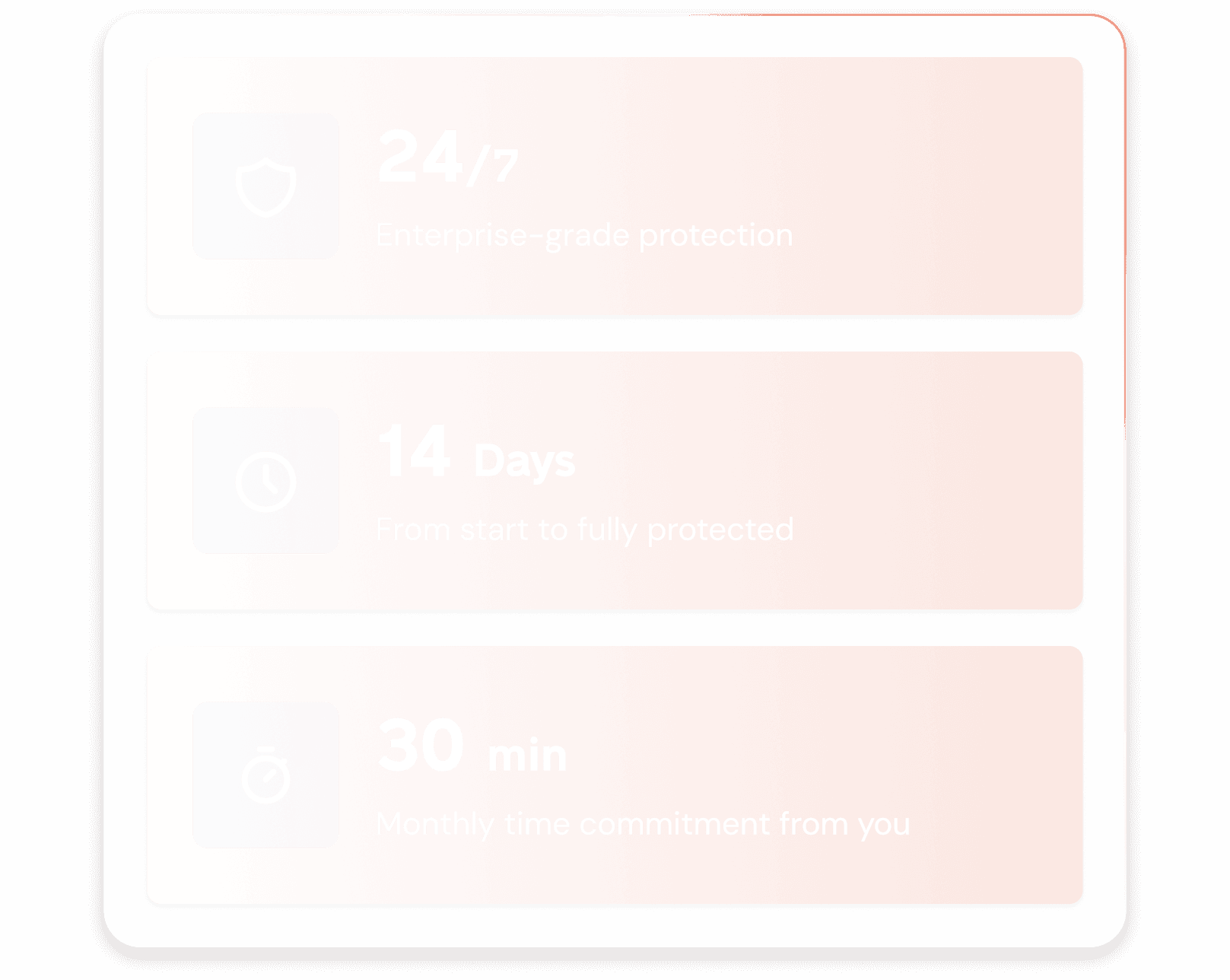
Your systems are monitored 24/7. When something looks wrong, we handle it.
- Suspicious logins get flagged immediately
- Malware gets blocked before it spreads
- Compromised devices get isolated in seconds
Your Entire Security Program. Done For You.
No piecing together solutions. No vendor juggling. One answer to the security problem — managed for you.

Security Frameworks & Compliance
SOC 2, HIPAA, ISO 27001, PCI, customer security questionnaires. We know what applies to your business and translate requirements into enforceable controls.
Continuous compliance. Questionnaires in hours.

Tools & Procurement
CrowdStrike, Okta, Jamf, Intune, Chrome Enterprise—procured at volume pricing. No enterprise minimums. No multi-year lock-ins. Licenses in your name.
The right tools. No guesswork.

Configuration & Best Practices
Configurations applied and enforced according to security best practices. Configuration drift detected and corrected. Updates and patches—handled.
Security that doesn’t decay.

Experts On Call
24/7 threat monitoring and incident response. Real security professionals detecting issues, triaging alerts, and handling problems as they happen.
Your security team, without the headcount.
What Our Customers Say
“That’s what we were paying for: to not have to worry about it anymore.”
Chief Information Security Officer
“Now we don’t have to waste time wondering what’s going on with our provider. We can be confident in Zip’s abilities instead of guessing all the time.”
Chief People Officer
Deep security expertise. Latest best practices. Built in.
Thousands of real-world deployments behind every recommendation. Fully operated so you can focus on your business. Explore our product features to learn more.
Device Management
Every laptop and phone enrolled, configured, and secured. macOS, Windows, iOS, Android.
- Remote wipe capability
- Automatic encryption
- Security policy enforcement
Identity Protection
MFA on every account. Single sign-on. No more password spreadsheets.
- Multi-factor authentication
- SSO integration
- Access management
Endpoint Security
CrowdStrike on every device. Enterprise-grade threat detection and response.
- Real-time threat prevention
- Ransomware protection
- 24/7 monitoring
Compliance & Audits
Pass SOC 2, HIPAA, and customer security reviews. Documentation included.
- Audit-ready reports
- Policy documentation
- Security questionnaire support
Employee Onboarding
New hires get set up securely from day one. Offboarding handled too.
- Secure device setup
- Account provisioning
- Access revocation
Data Protection
Know where your data lives. Control who can access it.
- Data loss prevention
- Cloud app visibility
- Access controls
Pass Audits and Customer Security Reviews
Zip deploys required controls, organizes your evidence, and handles incidents—so you're always ready.
Deploy Proven Security Controls
Your customers expect a minimum set of security controls. We deploy, configure, and manage them, so you’re ahead of requirements, not chasing them.
Communicate With Confidence
Don’t wait for the questionnaire. We help you build a security packet that puts you on offense—evidence organized, security posture documented, ready to share proactively.
Keep Incidents Contained
When something happens, we handle remediation and generate the report, with every detail captured, assessed, and documented. Incidents contained quickly. Fewer reportable events.
Don't Be Your Customer's Weakest Link
Attackers target smaller companies to reach their enterprise customers. Don't be the opening.
Attacker
Your Company
Enterprise Customer
Enterprise customers have invested heavily in their own security. Attackers know the easier path is through vendors and partners who haven't. That's why big companies are demanding more from their supply chain—and why you're in the crosshairs.
62%
of breaches originate through third-party vendors
Starbucks
went down because their scheduling software vendor got hacked
3x
more likely to be targeted—not for what you have, but for who you're connected to
Enterprise-Grade Security
We deploy the same security controls your enterprise customers require—endpoint protection, identity management, device security, compliance.
Fully configured. Fully operated. No weak links.
Common Questions
Answers to what we hear most often
You’re exactly the right size. 55% of ransomware attacks target companies under 100 employees. You have customer data, bank accounts, and fewer defenses. You’re ideal for attackers who prefer easy wins over hard fights.
Does your MSP use CrowdStrike? Enforce MFA on every account? Encrypt every laptop? Ask them for a security posture report. If they can’t produce one, you have your answer.
A single ransomware attack costs $170,000+ for small businesses on average. Zip costs less per month than one hour of a security consultant. And infinitely less than a breach.
We deploy in days, not months. We handle configuration, enrollment, and ongoing management. Your only job is to point us at your employees.
You can see exactly what’s protected: every device enrolled, every account with MFA, every endpoint with CrowdStrike running. No black boxes. No "trust us." Proof.
Vanta documents your security story. Zip puts the security pieces in place — and the documentation comes free. Pull it anytime. Tell a truthful story whenever you need it.
Get fully secure in 14 days
Book a 30-minute call to see how Zip handles your security end to end.