How Automated Enforcement Saves 20+ Hours a Week
Running security in a growing company often feels more like a cleanup than a strategy. Lean IT and security teams spend hours chasing device settings, following up on policy gaps, checking that automation tools and security systems still work as expected, and gathering evidence for audits or customer reviews. Each task matters, but together they pull time away from higher-value work.
Automated enforcement changes that. Instead of relying on manual checks and fixes, teams can keep approved policies enforced continuously in the background. The result is stronger security, less operational drag, and a program that is easier to run day to day. For lean teams, that often starts with a customized security plan that fits their environment, supports access control business operations, and helps them automate routine tasks across core IT systems.
Key Takeaways
- Manual security work quietly consumes hours every week across device checks, policy follow-up, and audit prep.
- Automated enforcement helps teams restore approved settings without the need for constant manual policing.
- Zip helps lean teams keep security controls visible, enforced, and provable across tools they already use.
Manual Security Creates More Work Than Most Teams Realize
For most small and mid-market teams, the problem is not a lack of effort. It is that security work grows faster than headcount.
Even in a well-run environment, someone still needs to ensure devices remain encrypted, patching stays current, endpoint protection remains active, and onboarding or offboarding does not create gaps. Then there is the proof problem: when a prospect, auditor, or customer asks for evidence, someone has to pause their work and gather it.
That work adds up quickly because it repeats. Teams revisit the same issues, fix the same kinds of drift, and answer the same questions in slightly different forms. Each task seems small on its own, but the interruptions compound.
Repetitive Security Tasks Add Up Fast
A typical week includes work like:
- Checking whether devices still meet policy
- Following up on missing encryption or patching
- Confirming endpoint protection stays active
- Reviewing onboarding and offboarding gaps
- Pulling screenshots or evidence for audits
The cost rarely appears as a single block on the calendar. It shows up as constant overhead.
The Problem Is Scale
This is where many teams hit a ceiling. Manual review cannot keep up with constant change. New devices appear. Employees change roles. Settings shift—tools update. Exceptions pile up.
Zip gives teams one place to see what is happening across devices and controls, then helps keep those controls enforced over time. That matters because security becomes much easier to run when it relies less on memory and manual follow-up from already stretched IT staff.
Why One-Time Setup Breaks Down
Security work often starts strong. Teams set policies, roll out tools, and properly configure devices. On paper, everything looks covered.
Then the environment changes.
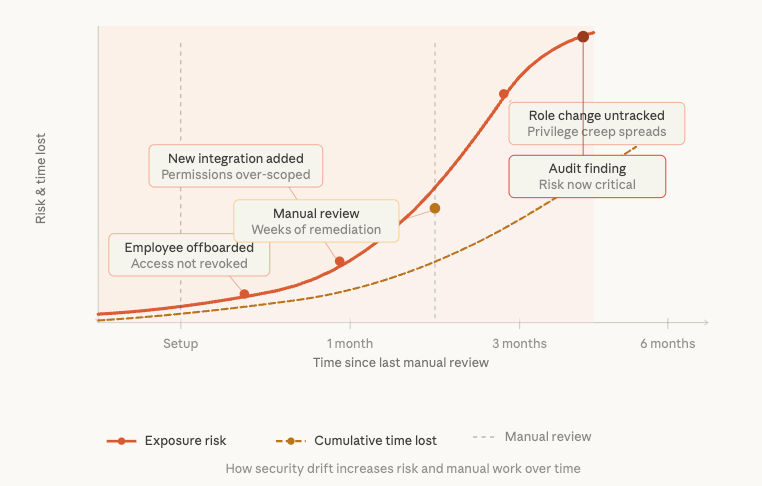
Security Drift Starts After Deployment
Drift starts the moment a live environment begins moving again. Devices miss updates. Settings change. New hires arrive with inconsistent setups. Coverage gaps appear quietly. The issue is not that teams made a bad choice on day one. The issue is that day one does not stay frozen.
This is why continuous monitoring and enforcement matter. NIST describes continuous monitoring as a way to maintain ongoing visibility into assets and the effectiveness of security controls, which is a much better fit for real environments than a one-time deployment mindset.
Silent Gaps Turn Into Expensive Work
The cost of drift is not only risk. It is also labor.
Someone has to find the gap, understand who owns it, decide what needs to happen, follow up, and then prove it got fixed. That cycle repeats every time a control falls out of policy. CISA has also highlighted how common misconfigurations, such as poor patch management, default credentials, and improper permissions, remain persistent sources of exposure.
Keeping Policies Enforced Over Time
Imagine a company that sets baseline device policies across Jamf and Intune. At first, everything looks consistent. Over time, settings drift across part of the fleet. A manual process means somebody has to catch that through a review, then work through the remediation device by device.
Zip continuously monitors compliance, surfaces where controls drift, and helps teams restore systems to the approved state faster. That reduces both the security gap and the amount of human cleanup work.
The New Model: Automated Enforcement That Keeps Working
Automated processes have a big operational impact. Instead of configuring a control once and hoping it stays in place, the team treats enforcement as continuous.
When enforcement becomes continuous, teams:
- Spend less time chasing routine issues
- Reduce inconsistencies across devices and users
- Gain clearer visibility into what is protected and what is not
- Build more confidence during audits, reviews, and customer questions
The old way relies on manual policing. The new way creates a more self-healing IT environment.
Why This Improves Business Efficiency
The immediate benefit is time savings. The deeper benefit is operational consistency.
When the team no longer needs to re-check the same issues every week, they can support growth without adding the same amount of repetitive work. That is a real business efficiency gain, not just an IT convenience. The right automation tools also help teams automate routine tasks, support cleaner handoffs across IT systems, and reduce repetitive, time-consuming work.
Self-Healing Security for Lean Teams
Zip helps teams move toward a more self-healing model by continuously enforcing controls, monitoring endpoint compliance, and making gaps visible before they turn into bigger problems. It does not replace the cybersecurity tools teams already trust. It helps those tools stay aligned and easier to manage over time.
That matters for more than visibility alone. A stronger operating model also supports anomaly detection, reduces the burden on IT staff, and automates workflows that would otherwise require constant manual attention.
Where the 20+ Hours a Week Go
Those 20+ hours rarely disappear into one major project. They get lost in repeated checks, follow-up work, and small fixes spread across the week. That is where automated enforcement makes a real difference: it reduces the frequency with which routine security work turns into manual cleanup.
1. Device Compliance Checks
Teams manually review encryption, patching, and baseline settings across the fleet. Even in a mostly healthy environment, someone still needs to confirm that devices remain compliant. Zip helps reduce that burden by keeping device and security policies enforced after deployment, so teams spend less time on repeated checks.
2. Policy Drift Remediation
Once a device falls out of policy, the work begins. Someone investigates the issue, contacts the user if needed, and fixes it. Then the cycle repeats with the next exception. Zip helps by continuously monitoring compliance and restoring approved settings more consistently, reducing repetitive remediation.
3. Endpoint Protection Verification
EDR cannot do its job if it is misconfigured, inactive, or unhealthy across part of the fleet. Verifying that coverage stays intact takes time, especially across multiple tools. Zip gives teams real-time visibility into endpoint compliance, so they do not have to jump between disconnected systems to see what is covered and what needs attention.
4. Onboarding and Offboarding Security Tasks
New hires need the right controls from day one. Departing employees should not leave behind unmanaged access or device gaps. In fast-moving teams, that becomes a recurring operational burden. Zip helps standardize and reinforce those workflows, so security depends less on manual follow-up.
5. Audit Evidence and Security Questionnaires
This is one of the biggest hidden drains. Proof work often starts from scratch, with teams collecting screenshots, exporting reports, and piecing together answers under deadline pressure. Zip helps teams maintain evidence over time, which makes audits and customer reviews easier to manage and less disruptive.
If your team spends too much time chasing routine security work, take a tour to see how Zip helps keep controls enforced over time.
Scaling IT Operations Without Scaling Headcount
As companies grow, they add more than devices. They add people, tools, locations, workflows, and compliance pressure. Manual security work grows with it all.
That is why lean teams do not need more dashboards to stare at. They need fewer tasks that depend on constant attention.
A better operating model standardizes device management and security workflows, enabling the environment to grow without multiplying repetitive work. That is one of the clearest business cases for automated enforcement: it helps teams scale operations without scaling headcount at the same rate.
What Automated Enforcement Should Look Like in Practice
Not every security platform solves this problem well. For lean teams, the right system should reduce manual work, improve visibility, and make security easier to maintain over time.
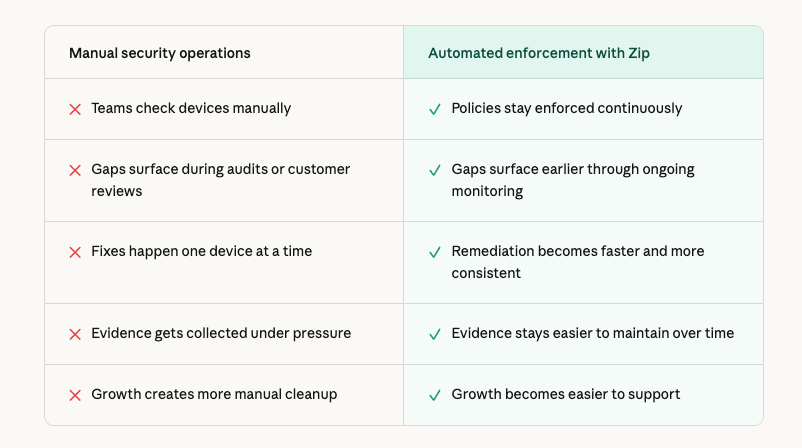
A strong automated enforcement solution should include a few core capabilities, including:
- Provide visibility across your existing tools, so teams can see what is happening across devices, identities, and endpoints in one place.
- Support continuous enforcement, not just alerts, so approved controls stay in place instead of drifting until someone notices.
- Make it easier to demonstrate the security posture for audits, customer reviews, and leadership questions.
- Fit lean teams by reducing operational load rather than adding another system that needs constant attention.
These priorities also align with broader industry guidance. CIS Controls emphasize continuously assessing and tracking vulnerabilities on enterprise assets, while CISA’s secure-by-design guidance encourages automation for monitoring and routine updates to reduce customer burden.
Stop Spending the Week Chasing Routine Security Work
Lean teams cannot afford to spend the week policing routine security issues by hand. As environments grow and change, manual work creates more drag, more inconsistency, and less confidence.
Zip helps solve that by giving teams a clearer view of what is happening, keeping controls enforced over time, and making security easier to run day to day. With the right combination of visibility, enforcement, and ongoing maintenance, teams can spend less time reacting and more time improving the business.
Discover how Zip’s endpoint security helps your team save time, maintain stronger security, and spend less effort on manual follow-up.
Frequently Asked Questions About Automated Enforcement
1. What is automated enforcement in IT and security?
Automated enforcement keeps approved settings and policies in place over time. Instead of relying on someone to manually check every device, the system identifies drift and helps restore the expected state more consistently.
2. How does automated enforcement improve business efficiency?
It reduces repetitive manual work, shortens response time for routine issues, and helps lean teams support more users and devices without adding the same amount of overhead.
3. Does Zip replace tools like Jamf, Intune, or CrowdStrike?
No. Zip works with the tools teams already use. It helps keep controls visible, enforced, and easier to prove across those systems.
Related articles

Why Automated CIS Benchmark Enforcement Is Stronger Than Manual Security

Ready to Work in Minutes with Zero-Touch Security