The Security Questionnaire Just Paused Your Deal. Here’s How to Be Ready Next Time.
If you haven't been asked about your security posture by a prospective customer yet, it's not because it won't happen. It's because you haven't closed the right deal yet. Zip surveyed 301 founders and technical leaders about how security requirements are showing up in the sales process.
The results are unambiguous: for modern businesses, security posture now affects sales pipeline.
Key takeaways
- Security requirements are now standard in enterprise sales, not an exception — 74.1% of companies have already been required to demonstrate specific security controls to close a deal.
- The bar has moved from policy to proof. 80.7% of enterprise buyers now audit for compliance rather than taking your word for it, which means documentation and evidence matter as much as having the controls in place.
- Companies that build security visibility before a deal is in motion handle vendor reviews faster and with less scrambling than those who start looking when a questionnaire arrives.
Don’t have time to read this blog? No sweat. We made it into a podcast for you:
The Numbers Don't Leave Much Room for Debate
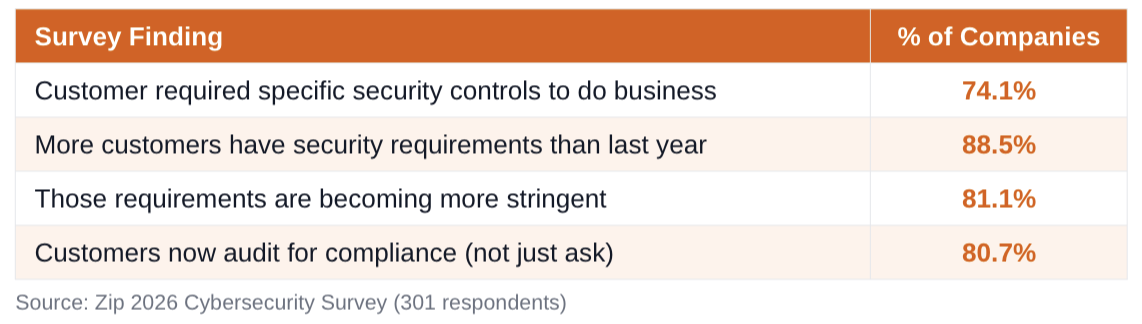
Nearly three in four founders say a customer has already required specific security controls just to do business with them. And 88.5% say those requirements are increasing year over year.
If you're building a company that sells to enterprises — or hopes to — this is your operating reality.
Security Reviews Are Showing Up Earlier in the Funnel
Here's the moment most founders recognize: you're two weeks from a signed contract, and procurement sends a 150-question security questionnaire. Everything pauses. Your team scrambles to figure out what you actually have documented, what controls you've actually implemented, and whether the answers you want to give are actually true.
That's not a one-off. That's just what standard enterprise onboarding looks like now.
Customers are asking vendors to demonstrate things like:
• Device security controls and endpoint protection
• Identity and access management practices
• Monitoring, logging, and incident response procedures
• Compliance with recognized security frameworks
• Internal security policies and how they're enforced
These questions arrive as security questionnaires or vendor risk assessments, and they've become a routine step in enterprise procurement, not an exception.
Security review on your desk already and you’re not sure where to start? Check out our blog “How to Answer a Security Questionnaire Without a Security Team.”
Why This Is Happening Now
Three forces are converging to make vendor security scrutiny the norm:
First, software vendors are more embedded in critical workflows than ever before. When a vendor has access to sensitive data or is integrated into core systems, its security posture becomes the customer's risk. Customers know this.
Second, organizations face their own compliance obligations. Many security frameworks (SOC2, ISO 27001, HIPAA, and others) explicitly require companies to evaluate the security practices of their vendors. When your customer is getting audited, you get audited too.
Third, supply chain attacks have made vendor risk real and visible. The days of "we trust our vendors" are over. Security teams have mandates to verify, not assume.
The Most Important Shift: From Policy to Proof
This is the finding that should change how you think about your security program:
80.7% of respondents say customers now audit for compliance. They don't just ask if controls exist, they verify your team can actually implement and enforce those controls.
That distinction matters enormously. It means telling a customer, "we have an endpoint security policy," is no longer sufficient. They want to see evidence. That means documentation, logs, certifications, and in some cases direct access to your security posture during the review process.
For growing companies, this is an operational shift. You need to be able to demonstrate your security controls, not just describe them. In short, paperwork alone no longer cuts it.
What This Means for Your Company
The companies that handle security reviews well aren't necessarily the ones with the most sophisticated security programs. They're the ones who can answer questions quickly and confidently, because they have visibility into what's actually happening across their environment.
That means knowing:
• Which devices are accessing your company's systems
• Whether those devices meet your stated security requirements
• Whether your policies are consistently enforced, not just documented
• Where your gaps are, before a customer finds them
Companies that prepare for this before they're in the middle of a deal are in a fundamentally different position than those scrambling to answer a questionnaire mid-negotiation.
How Zip Helps
Zip Security gives companies the visibility they need to answer security questionnaires confidently and pass vendor reviews without last-minute scrambles.
By connecting identity systems, devices, and security controls in one place, Zip lets you see which devices are accessing company resources right now, and whether they actually meet the security standards you're claiming they do.
That's the difference between saying you have security controls and being able to prove it.
Want to bridge that gap before your next security review? Book a demo with Zip today.
Related articles

How Intrusion Prevention Systems End Alert Fatigue

Fixing the Hidden Gap in Security With Autonomous Monitoring