The Automated Onboarding Process Your Growing Teams Need
An automated onboarding process is a repeatable system that deploys a new hire's device, applies baseline security controls, provisions the right access, and provides proof that everything works—without relying on manual checklists. Onboarding automation makes that system consistent at scale.
As your team grows, onboarding speed often improves first. You ship laptops faster, send invites sooner, and get new hires up and running on your operating systems on day one. But quality slips in quieter ways: a Mac ships without full enrollment, an endpoint agent installs but never checks in, or access goes live before the device meets your baseline. Nobody tries to cut corners. The process can't keep up with the volume.
Zip helps teams standardize onboarding across Jamf and Intune so "ready on day one" means "secure and policy-compliant," not just "able to log in."
Key Takeaways
- An automated onboarding process makes the process repeatable, so new team members start with a secure, consistent setup while improving the overall employee experience.
- Standardize device deployment across Mac and Windows and use zero-touch enrollment to reduce manual work, saving time and reducing exceptions.
- Zip helps teams see, enforce, and prove onboarding controls across tools like Jamf and Intune, without relying on heroics.
Why Onboarding Breaks at Scale
Most onboarding programs fail the same way: they work at low volume, then buckle under operational load. For IT managers' security, the causes are common and fixable.
Mixed OS Fleets: Split Your Workflow
Jamf for macOS and Intune for Windows both work well, but they don't behave like one system. If you don't define what "ready" means across both platforms, your onboarding process splits in two—and those two tracks drift apart.
Enrollment Gaps Show Up Late—or Never
A device can look fine to a new hire while it misses enrollment steps, profiles, encryption checks, or security tooling. You often discover the gap weeks later during an audit, a customer questionnaire, or a "why doesn't this device show up?" investigation.
Drift Starts Immediately After Setup
Updates roll out. Users change settings. Profiles fail to apply. Security agents stop reporting. Without continuous enforcement, the baseline you set during onboarding starts to erode.
Ownership Stays Unclear
HR owns the start date. Managers own ramp. IT owns the device. Security or an MSP owns controls. When something slips, nobody knows who owns the fix.
Here's the key reframe: the problem is operational load. You don't scale onboarding with more spreadsheet tabs. You scale it by treating onboarding as a bounded system with clear status, clear owners, and controls that hold.
A single view shows what's enrolled, what's compliant, and what's missing across tools, so gaps don't stay invisible.
Manual Processes vs. Automated Onboarding
What Manual Onboarding Looks Like
A manual employee onboarding process usually relies on "done once" work:
- Checklists and tribal knowledge
- Delayed setup and last-minute fixes
- Inconsistent baselines between hires and roles
- Access granted before you verify device state
- Evidence gathered later (screenshots, spreadsheets, one-off exports)
Manual onboarding also tends to create unnecessary paperwork—even when the company operates fully online—because teams document steps after the fact rather than capturing proof as part of the workflow.
This approach breaks for one simple reason: it depends on humans noticing problems at exactly the right time. In a growing environment, that moment often passes quietly, and the gaps show up later as lost productivity and longer onboarding time.
What Automated Onboarding Looks Like
Employee onboarding automation turns those steps into a repeatable workflow:
- Consistent device deployment steps
- Zero-touch enrollment where possible
- Baseline controls are applied automatically
- Clear pass/fail readiness status
- Access management aligned to enrollment and compliance milestones
- Evidence available by default, not collected later
Automation removes avoidable work. Your team still defines the baseline. The system applies it, verifies it, and keeps it enforced.
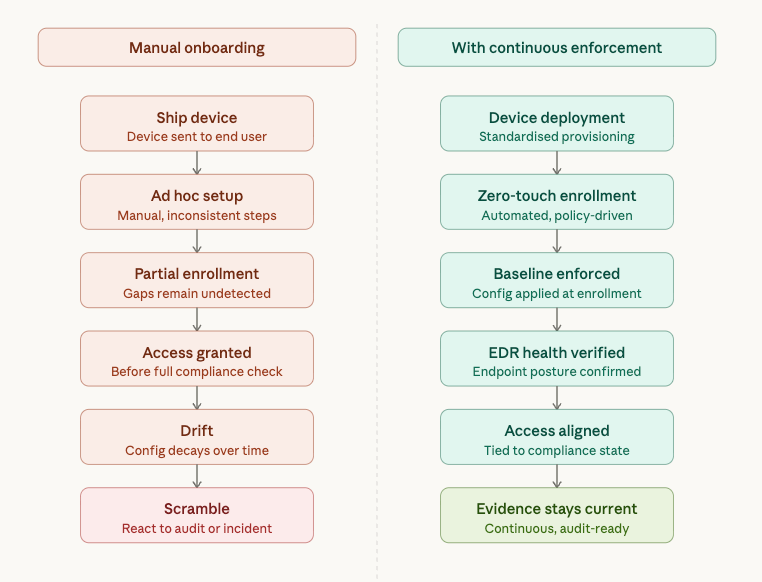
Zip turns onboarding into a bounded workflow: enroll devices, enforce baseline controls, verify EDR health, and surface exceptions with clear owners.
The Blueprint: Core Components of a Secure Automated Onboarding System
You don't need a perfect program to start. You need a baseline you can run repeatedly and a way to keep it true after day one. Focus on the essential steps that make onboarding secure and provable, then expand from there.
Step 1: Device Deployment With Zero-Touch Enrollment
Zero-touch enrollment lets a new hire power on a device and have it automatically enroll in management, apply required settings, and install needed apps—with minimal manual work from IT.
Start by standardizing what you can:
- Approved device models and OS minimums
- A Mac flow (Jamf) and a Windows flow (Intune) that produce the same "ready" outcome
- Role-based baseline apps and settings
Then automate the steps that create most of the manual load:
- Enrollment and configuration profiles/policies
- Baseline checks (encryption, updates, firewall, screen lock, etc.)
Finally, measure the basics:
- Enrollment completion rate
- Time from delivery to "policy-ready."
With Zip, you can run one onboarding standard across Jamf and Intune, so Mac and Windows onboarding doesn't become two separate systems.
Step 2: Continuous Enforcement
Updates, role changes, and exceptions create drift—even when your tools work exactly as designed.
Controls that commonly drift include:
- Encryption status
- Patch posture
- Local admin access
- Required settings and policies
Your goal isn't constant manual checking. Your goal is a system that keeps baselines enforced and makes exceptions visible early.
Zip continuously checks baseline controls and flags drift before audits, or customers force a scramble.
Step 3: Identity and Access That Matches Device Reality
You don't need deep IAM theory to improve onboarding security. You need one simple rule: role-based access only works when you know the device state.
Common failure modes show up fast:
- Access granted too early (before enrollment and baseline controls apply)
- "Temporary" exceptions that never get removed
A practical approach:
- Tie access workflows to enrollment and compliance milestones
- Track exceptions with an owner and a deadline
- Use "device compliant" as a gate for sensitive access where it fits your environment
By connecting device trust and identity context, Zip helps you quickly spot cases where "access is live, but the device isn't compliant."
Step 4: Endpoint Security That's Installed and Working
Onboarding often stops at "agent deployed." That isn't enough. You need to confirm:
- Sensor health (it runs and reports)
- Coverage (including every device)
- Enforcement posture (it matches your intended configuration)
During rapid hiring, small coverage gaps compound quietly. You end up with pockets of unknown protection that become hard to explain later.
Zip makes EDR coverage and sensor health visible across the fleet, so onboarding doesn't create "unknown coverage" pockets.
Step 5: Audit-Ready Evidence Without Extra Work
Avoid "automated compliance." The better promise is provable controls.
Evidence that matters for onboarding includes:
- Control coverage by device group and role
- An exceptions list with owner and status
- Proof that controls stay enforced over time—not just on day one
Automating evidence reduces the scramble when audits, customer security reviews, or questionnaires show up. It also reduces manual document management by keeping proof in the system rather than scattering it across email threads, spreadsheets, and screenshots.
Zip keeps evidence current, so security reviews and questionnaires don't turn into a screenshot project.
Common Pitfalls And How to Avoid Them
- Automating a Messy Process: Standardize first, then automate—this keeps the onboarding experience consistent across roles and teams.
- Treating "Enrolled" as "Secure": Enrollment is a step, not an outcome—verify baselines.
- Ignoring Drift and Exception Handling: Define how you track, own, and close exceptions.
- Unclear Ownership of Failures: Assign owners by task and by exception type.
- Rolling Out Without Metrics: Measure time-to-secure-ready and exceptions to improve.
A control plane reduces unknown unknowns by surfacing control gaps and assigning clear status, so you don't discover issues weeks later.
Implementation Roadmap for Growing Teams
Here's a sequence that fits lean capacity and scales smoothly as you onboard new employees:
- Map your current onboarding flow (tools, owners, breakpoints)
- Standardize device deployment paths (Mac + Windows)
- Define baseline controls and verification checks
- Operationalize endpoint security health checks
- Connect access workflows to device readiness milestones
- Phase rollout by role or team, then expand
Zip helps teams roll this out in phases while keeping the baseline consistent across Jamf/Intune and endpoint security tools.
From First Login to Continuous Control: The Onboarding Shift
Onboarding is where drift and control gaps often begin—especially when each new hire triggers manual steps across device management, identity, and endpoint security. An effective onboarding process treats it like a repeatable system, not a checklist: standardize device deployment, use zero-touch enrollment where it makes sense, and continuously enforce baseline controls so "ready" becomes a provable state.
If you want onboarding that stays consistent as you grow—across Jamf, Intune, and endpoint security—Zip can help you make it enforceable and provable. See how Zip supports device management today.
Frequently Asked Questions About Automated Onboarding
1. What Is a Zero-Touch Enrollment Process?
Zero-touch enrollment lets a new hire set up a company device with minimal manual work from IT. When the device powers on, it enrolls in your management platform (such as Jamf for macOS or Intune for Windows) and automatically applies required settings, apps, and security policies.
2. How Is an Automated Onboarding Process Different From a Checklist?
A checklist lists what should happen. An automated onboarding process ensures those steps are completed consistently and maintains key controls after day one. It standardizes device setup, verifies readiness, tracks exceptions, and creates a clear "ready" state you can prove.
3. Does Zip Replace Jamf or Intune?
No. Zip does not replace Jamf or Intune. Zip sits above the tools you already use and acts as a control plane—helping you see onboarding status in one place, keep baseline controls enforced over time, and make results easier to prove for audits and customer reviews.
Related articles

Why Automated CIS Benchmark Enforcement Is Stronger Than Manual Security

Ready to Work in Minutes with Zero-Touch Security